The Covid-19 pandemic forced authoring teams to collaborate online to ensure successful delivery of high-stakes exams. This way of working has become the ‘new normal’ for many.
There are, however, security risks associated with the efficiency and convenience of authoring tests using standard office programs.
In this guide our Chief Technology Officer, Jim Allen, outlines the 3 most common security risks in exam authoring, and how your awarding organisation can address them.
Security Risk 1
Exam content being held in vulnerable systems during development
Your exam content likely passes through multiple review steps during development. With each step, the content may move from one system to another, such as an email, a Word document, or a printed piece of paper.
Each step represents a potential point of vulnerability. When your content is developed in multiple places there are more access opportunities for attackers to exploit.
There is also an increased risk of errors creeping in and corrections being missed when versions of documents are held in different places.
Some of the most common places sensitive content can unnecessarily linger are:
- Email inboxes
- Instant messenger (Teams, Slack, Skype, or WhatsApp)
- Folders on local devices
- Online file sharing (GoogleDocs, SharePoint, or DropBox)
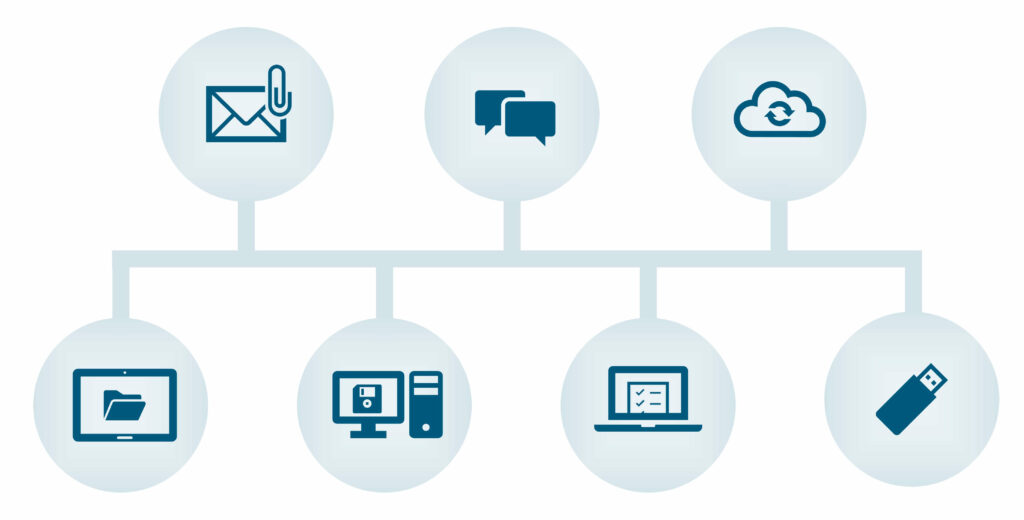
Storing and moving content between these systems adds increased complexity and unnecessary risk to your workflow. Risks may include internal staff given unauthorised access to confidential information, or even ransomware attacks where cyber criminals gain access to your systems and lock your data.
How to improve security during question development
If assessment content is being held on any of the shared systems listed above, there should be organisation-wide security processes to reduce security risks, such as:
- Implementing policies for where files can be edited or prohibit downloading of sensitive materials to devices
- Train staff to spot risky emails or unsafe websites
- Run and keep security products up-to-date on all devices
- Make sure operating systems are patched and up-to-date
- Make sure internet browsers are current and updated
- Have your IT systems audited and certified, for example through ISO 270001 certification
- Run regular penetration tests, ideally conducted by external experts
The simplest way to reduce the risk of unauthorised access is to maintain and process your sensitive data in a separate authoring and test building system. This will significantly reduce the number of transit points.
The UK’s National Cyber Security Centre website provides further information and guidance on cyber security improvements for businesses.
Security Risk 2
Weak account security putting exam content at risk
For most users, the ability to auto-login is a welcome convenience, and it is now very easy to store usernames and passwords on your browser.
Using these features will significantly increase the risk of an exam breach should someone fraudulently gain access to your device. But even if you switch off auto-login, having a password as a single layer of protection to an account does not necessarily make it secure.
The most common route of unauthorised access to IT systems is via an external attacker using valid credentials.
How do people steal these credentials?
Phishing attacks are common and a highly effective way of gaining usernames and passwords to systems. A substantial number of high-profile data breaches have also made usernames and passwords public for hackers to use.
Brute force attacks (where passwords are guessed) are less effective but still a risk because people often use the same passwords on multiple systems.
Passwords cannot be relied on as the only security step for highly confidential data.

It’s not always immediately obvious if your passwords have been compromised. You can check to see if your data has been involved in any security breaches on the ‘have i been pwned’ website.
How can an awarding body improve its password security?
The most secure systems use two-factor authentication to protect against user login credentials being used fraudulently. This system of account protection is becoming increasingly common in account security and you may already use it to access platforms which contain sensitive data, such as online banking.
What is two-factor authentication?
Two-factor authentication requires a user to enter the correct username and password combination, and enter a unique, randomised one-time code from a text or an app. This makes it impossible for someone to successfully impersonate a user without having access to their mobile device or the software that generates the unique random security code.
Two-factor authentication is now the best way to protect your assets, questions, and tests.
Security Risk 3
Internal access to sensitive materials going unchecked
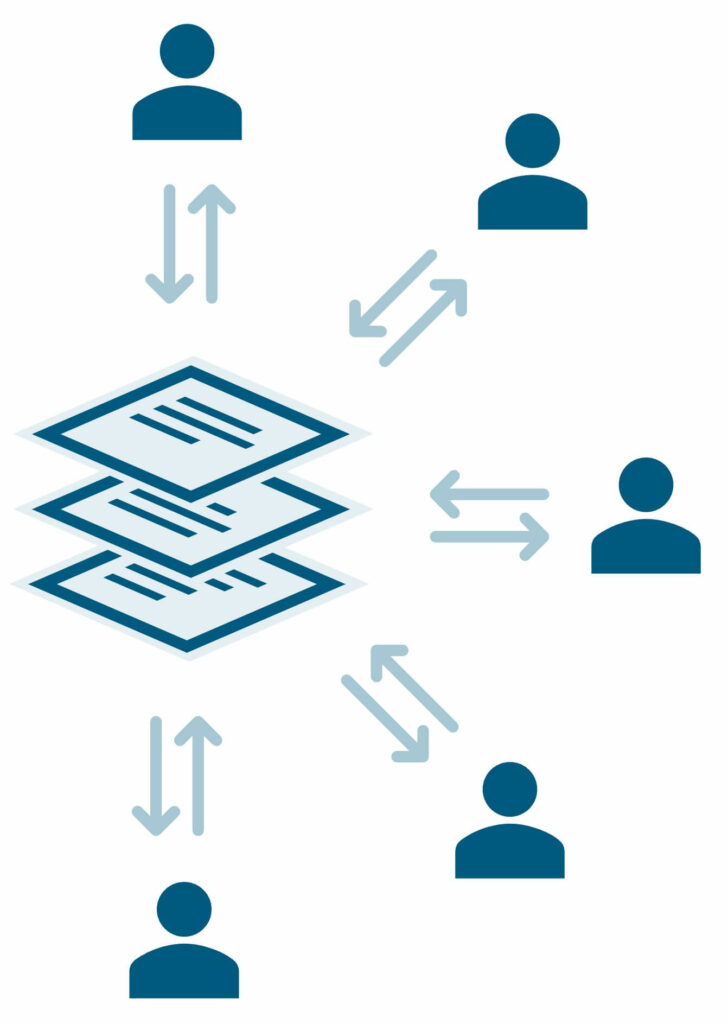
Too many users having access to sensitive information is a common problem. Ideally, questions and papers in development should only be accessible to those who are working on them. They should not be able to make changes outside their remit, and items should only be visible at the time they are working on them.
However, restricting user access to the degree required can be complex and time consuming in existing systems.
Most file sharing systems do not easily facilitate granular restrictions as they are designed to promote sharing, not reduce it. It is therefore challenging to create and maintain a file sharing environment where relevant content is accessible to only certain people, to perform particular actions, at specific stages.
Keeping on top of these permissions settings in conventional file sharing and office programs presents challenges. It requires a lot of set up and needs manual changes for every stage of each workflow. As a result of this, projects can be delayed.
In the UK, the recent Ofqual G4 regulations are specifically aimed at addressing user access issues. They require British awarding bodies to ensure practising teachers who author exam questions do not know if their content will be on the final test.
Teachers being able to give unfair advantage to their students is just one way in which an unsophisticated user permissions set-up can undermine test security.
How can exam developers improve their user permission control?
You can solve these access problems by moving away from file sharing sites to a system dedicated for test building. The user permission settings on authoring systems like GradeMaker give you tools specifically designed for easily granting and restricting access during the test development process.
You can automate the access given to each user at every stage of a workflow, enabling questions and papers to move between stages faster. This gives you complete oversight and control at every level and allows you to audit what users have seen, created, changed, or deleted in the event of a leak. This extra accountability also acts as a deterrent and provides opportunities to trace any other potentially compromised assets.
Watch the Quick Look video below to see how we have designed a system to make a more secure exam authoring workflow possible.
Jim Allen
Jim has worked in software development for over 20 years, specialising in enterprise scale software and implementations.
As Chief Technology Officer at GradeMaker, he directs the development team in creating user friendly tools to improve the complex processes of high-stakes test authoring.